Backup Appliance
Our Backup Appliance named Accordion is a self-contained device that can utilize any external storage for backing up your data, files, pictures and documents. The appliance manages backup-software and hardware components within a single device. Backup your entire user's data, pictures, documents and you will always be prepared when data restoration is needed. Regardless of what type of machine and/or Operating Systems our Backup Appliance can be used to back up your critical data.
Backup Multiple Users
Backup your entire user's data, pictures, documents and you will always be prepared when data restoration is needed.
Home
Backup Appliance is ideal for the home.
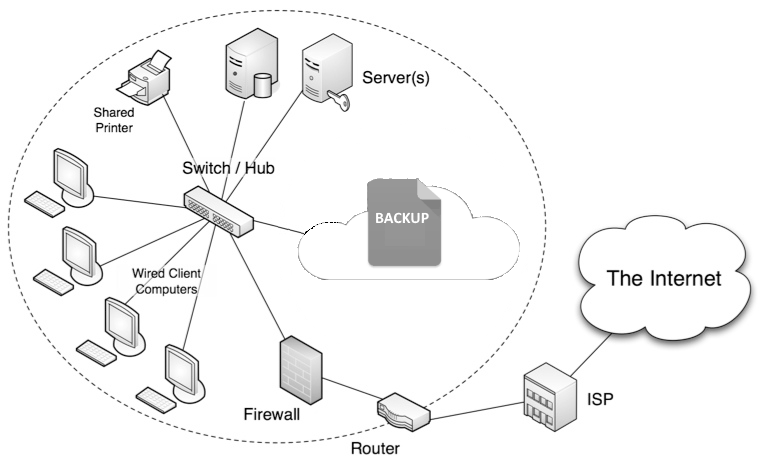
Business
Backup Appliance backs up all your worstations at work.
Quick Restore
Restore in hours instead of days. Restore full, partial, multiple folders, files and versions of your data. Historical data is only limited by your storage you choose to purchase.
Ransomware
Our Backup Appliance can protect against ransomware by segregating the way backup is handled.
Software on board
Unique feature of our device is that there is no local software to install for Accordion to work.
Multiple Operating Systems
With a single device, you can backup multiple Operating Systems such as Windows-Desktops, Windows-Servers, macOS, and all flavors of Linux.
Overview
Accordion backup appliance is a pocket sized, light weight device that can be connected to any USB external hard drive to backup your data to. If your data is too large for your backup, simply plug in another external hard drive or unplug existing hard drive with a larger drive. The Accordion custom operating system gives you additional protection against virus and spyware because the backup drive is not seen on your network.
Specifications
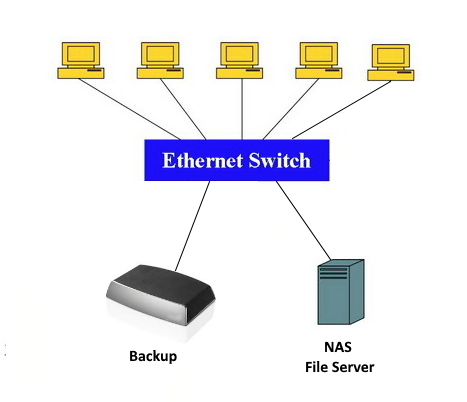
Accordion Backup, allows for creation of multiple backup scenarios.
- Backup multiple PCs, Macs and Linux machines to a single Accordion appliance.
- Backup any number of Operating systems; including Windows, MacOS and Linux
- Backup all your network and office users
Accordion Recovery
- Fast recovery for data, hours instead of days
- Manage your own hard disk sizes based on your specific needs
- Not beholden to outside cloud bandwidth throttling
Flexibility and Security
The Accoridon backup appliance is small enough to fit in your shirt pocket and light enough that you won't even know that it is there. It has no moving parts and runs so cool that a fan isn't needed. The Accordion can connect wired or wireless to any network. In the unfortunate event that the Accordion appliance is lost or stolen, there is no need to worry because it stores no data on its own, there is no security risk at all.
Turn your Raspberry Pi into a print server
According to WIkipedia's Internet Printing Protocol, Internet Printing Protocol ( IPP ) is a specialized Internet protocol for communication between client device and printers or print servers[2]. IPP uses HTTP as its transport protocol. Each IPP request is a HTTP POST with a binary IPP message and print file, if any, in the request message body. The corresponding IPP response is returned in the POST response. HTTP connections can be unencrypted, upgraded to TLS encryptio ...
Using Raspberry Pi as Thin Client
A thin client, or lean client, is a type of computer that relies entirely on its network connection to accomplish tasks. A typical laptop or desktop PC—otherwise known as a fat client—has the memory, storage, and computing power to run applications and perform computing tasks on its own. A thin client, on the other hand, functions like a tv; it only needs to draw the screen and render the sound. The actual computing power residing on a networked host ( or server ). The hosts may be on-site ...
Installing WordPress on Raspberry Pi
In this article, we will be showing you how to set up a WordPress server. According to W3Techs, WordPress powers over 40% of all the websites on the Internet[1]. More than one in three websites that you visit are likely powered by WordPress. For CMS, or content management systems, almost every 2 out of 3 CMS websites uses WordPress[2]. In order to install WordPress, you need a web server stack. In this article, we will go through setting up ...
Set UP Static IP
A static IP address, or fixed IP address, is an IP address that never changes. Not everyone needs a static IP address. Static IP addresses are necessary for devices that need constant access. For example, a static IP address is necessary if your computer is configured as a server, such as an FTP server or web server. If the server was assigned a dynamic IP address, it would change occasionally, preventing your router from knowing which computer on the network is the server. In this article, ...